Show Your Work: VulnHub Raven & DC:1
I’ve been reading a lot of VulnHub walkthrough posts recently, and most of them are quite useful and interesting. The challenge I noticed, is that most of them are written from the perspective of a (sometimes highly) experienced security professional. For the novice, we may not always have the experience to understand why certain assumptions were made, and can’t always see clearly HOW the experienced professional decides things like which tools to use.
For most of us, when we were in elementary school, we were expected to show our work when solving problems in math class. While it may not have been fun at the time, as a sometimes-teacher I can appreciate the value of it from an evaluative as well as pedagogic perspective. Thus, this post (and hopefully more in the future) is my attempt to use that model to improve my self-education efforts.
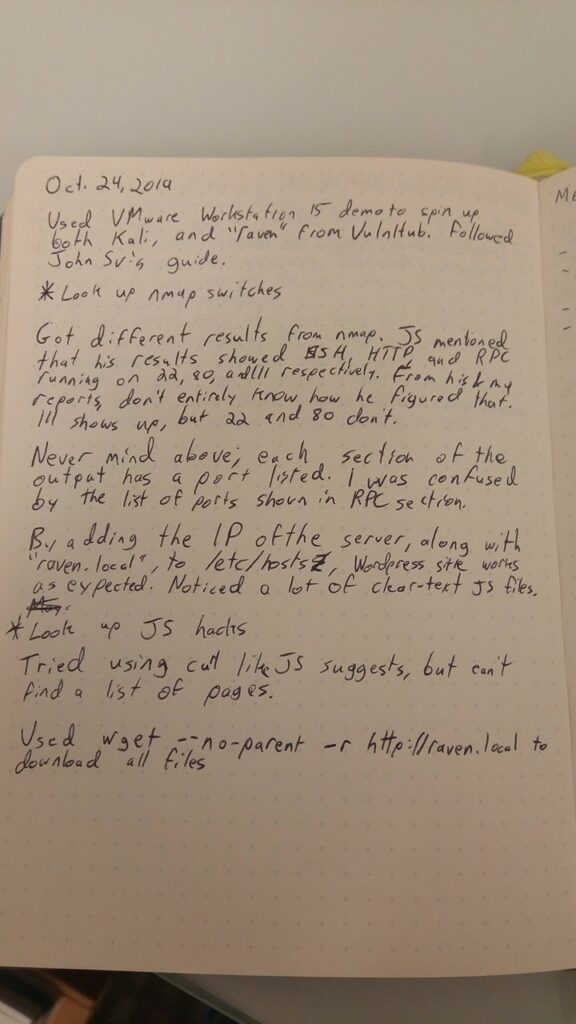
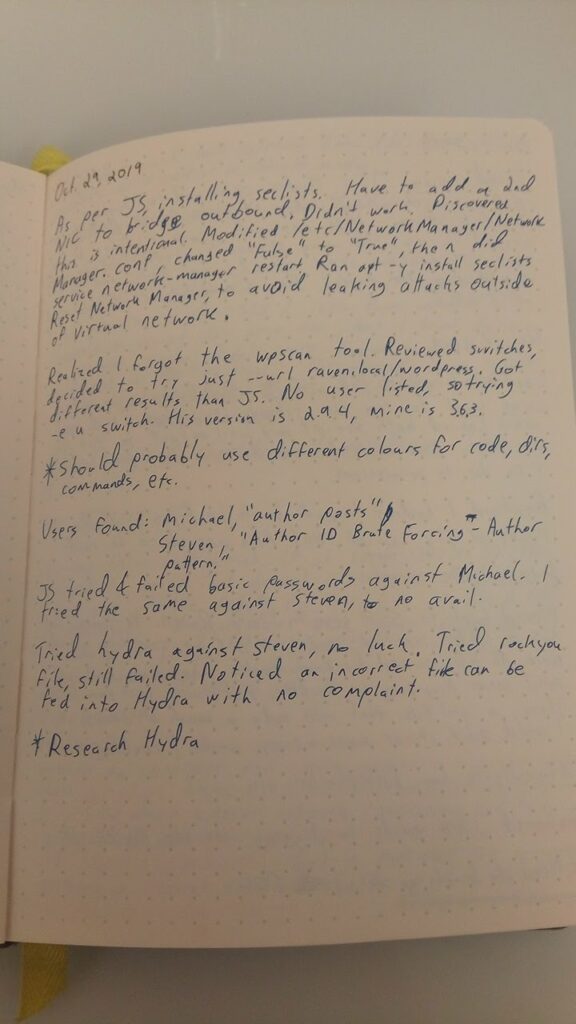
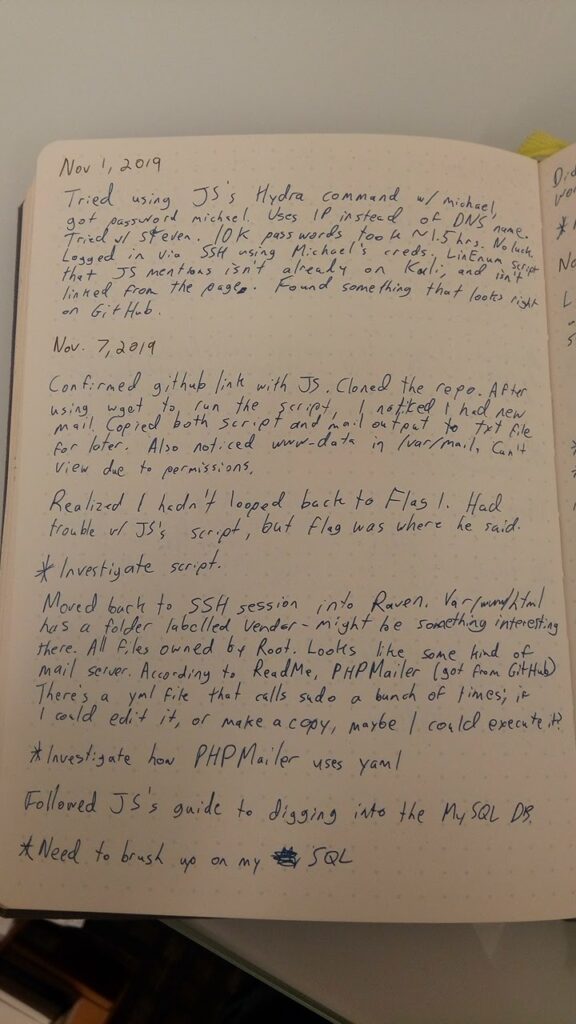
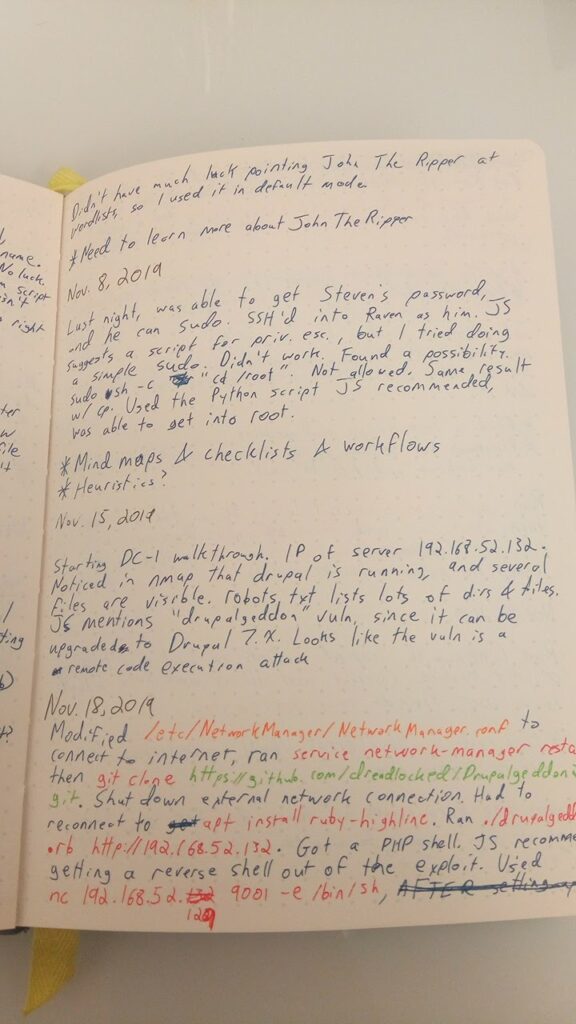
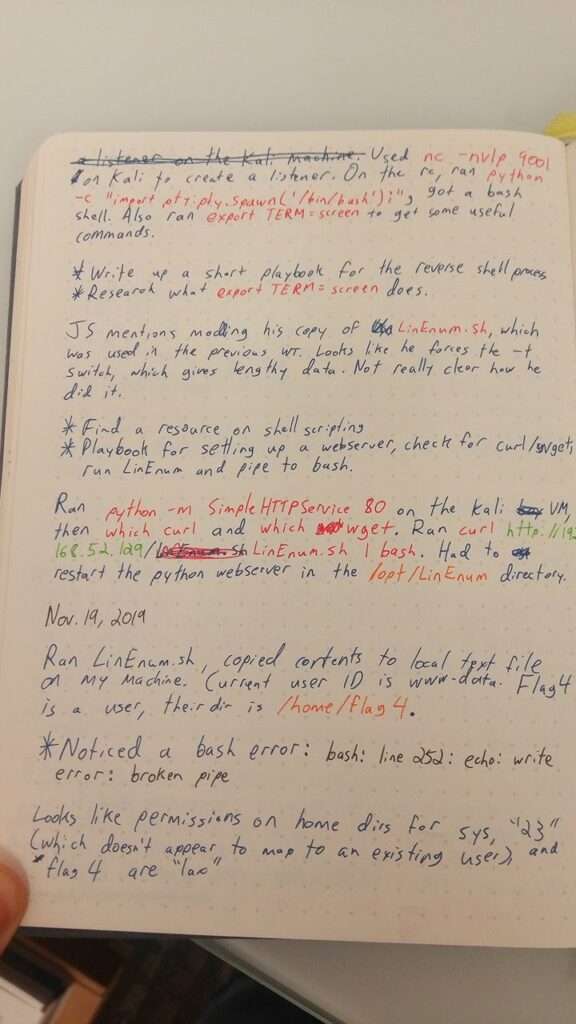
John Svazic, of Purple Squad Security fame, started a series this summer in which he was working through various VulnHub machines. I decided to do a kind of work-along, to see where my skill-level was at. Work went a bit slowly, since I had to fit this in between all the other tasks on my plate. That being said, I’m really happy with how this went.
So, without further ado, here are my notes from the first two (and the start of the third) VulnHub work-alongs.
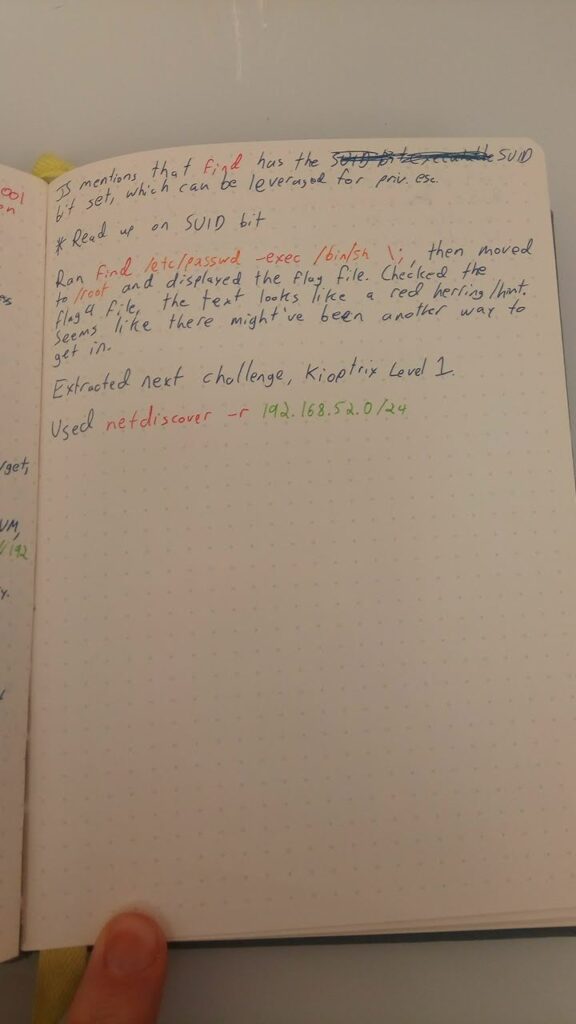
I’m in the process of working through John’s next walkthrough: Kioptrix Level 1. Hopefully I’ll manage to get enough time to post a set of notes for that before the end of December.
Leave a Reply